Example of Using a Cybersecurity Standard: Applying IEC62443 in Aveva System Platform Environments
How cybersecurity standards can help us define our path to protect communication infrastructures from potential threats.


In this post, we will see how cybersecurity standards can help us define our path to protect communication infrastructures from various potential threats that may occur.
To do this, we will use part of the standards defined in IEC 62443, the de facto standard for the protection of industrial environments and ICS automation.
As an introduction to the standard, I recommend reading this entry where the basic concepts, protection levels, and fundamental cybersecurity requirements are explained.
Specifically, the IEC62443-3-3 document explains in detail the different security controls to be implemented for each of the fundamental requirements (FR) and for each target security level (SL-T).

Summarizing and providing practical examples of these countermeasures in a SCADA environment, we obtain the following table of protection measures that we can adopt for each of the security levels:

Step 1: Identify Zones and Conduits
The first step is to understand the installation to be protected:
- What zones do I have? What processes do I have? Which are the most critical?
- Which are the equipment that support the process? How do they communicate?
- What are the communication flows between zones?
- Is it updated?
- What threats do I have?
- What are the levels of protection that I need? (being realistic vs. the investment to be made)
It is usually a good idea to carry out cybersecurity audits that provide a realistic picture of the current state of the environment.
Step 2: Network Segmentation Design
The network architecture will determine the ease or difficulty of applying many of the recommended security controls. There is no “correct” or “incorrect” network architecture, but the standard does offer us a set of models that can help us define a topology that is modular and scalable.
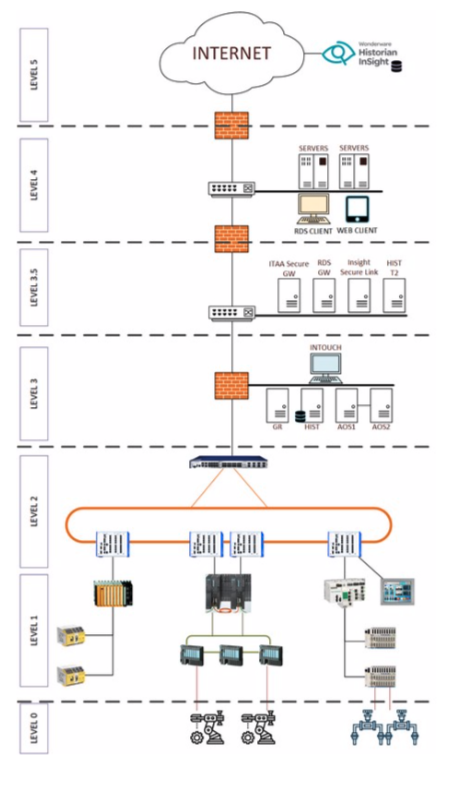
In the initial architecture, IT is perfectly separated from OT, and the industrial part is segmented into several levels:
- Level 3.5: DMZ where the services that will be accessible from non-process zones that require data for decision-making are hosted.
- Level 3: server area, global supervision, and production management.
- Level 1-2: network distribution area to the different process zones. This level is likely to be further segmented depending on the size, number of processes, etc.
- Level 0: process with its field buses.
Step 3: Definition of countermeasures to implement
Depending on the desired security level (SL-T) and the achieved level (SL-A), more or fewer countermeasures will be applied to increase the level.
The countermeasures to be applied can be of various kinds: technical, administrative, physical, legal, etc.
SL-T = 1
- DMZ as a front-end for remote access (Intouch Access Anywhere Secure Gateway, Insight Secure Link, Remote Desktop Services Gateway, etc.)
- Segmentation of level 3 network according to the objective: development subnet, supervision subnet, and Aveva server subnet
- Segmentation of process zones: Safety, critical process subnet
- Installation of Firewalls for the control of incoming and outgoing communications from each subnet.
- Application WhiteListing installation.

SL-T = 2
- Infrastructure subnet with account management, log, and backup servers
- Addition of sensors for the analysis and profiling of network traffic to detect anomalies in communications (NIDS)
- A centralized server for antivirus management is added in the DMZ
- A centralized server for controlled distribution of security patches is added in the DMZ
- Antimalware is added to the main servers.

SL-T = 3
To increase the security level, the following is added:
- GPS time server in the infrastructure zone.
- Mobile and tablet management server (MDM).
- SIEM server for the correlation and detection of cybersecurity events.
- Automated PLC/SCADA backup server.
- Use of VPN with two-factor authentication.
- Industrial communications hub with secure protocols (OPC-UA)
Step 4: Maintenance and adaptation to new needs
The threats, vulnerabilities, processes, technologies, people, etc. change over time, and with it, cybersecurity risks increase if nothing is done.
To maintain the security levels achieved, we must not forget to:
- Design our industrial network and its components in a redundant way to guarantee the high availability of all the components that enable the process.
- Monitor the systems for early detection of possible anomalies.
- Have a disaster recovery plan to be able to react and correct any anomaly in an efficient manner.
Conclusion
In this way, we see how cybersecurity standards, such as IEC62443, help us to structure and define how to address cybersecurity in a holistic way. This does not avoid the need to know the real state of the facilities and evaluate what would be the best changes and countermeasures to implement.
From Logitek, we can help you in this regard with our audit services and in-depth defense strategy.

