The New Era of OT Cybersecurity: how to Protect Yourself from 0-Day Attacks and Invisible Threats
What should the new generation of cybersecurity defenses for OT be like? We tell you in this post.


OT Cybersecurity, in the Spotlight
OT systems are increasingly exposed to advanced cyberattacks. Digitalization has opened new doors for attackers, who are increasingly using more sophisticated techniques. Techniques that current cybersecurity solutions are failing to stop, placing critical infrastructures in a vulnerable position.
If one thing is clear, it is that threats are evolving faster than defenses. An example of this is 0-Day attacks, which exploit unknown vulnerabilities before patches or protection measures exist. And what in an IT environment would translate into compromising data or interrupting digital operations, in OT can mean the paralysis of an entire production plant, to understand us.

Invisible Cyberattacks that Leave No Trace
The most recent attacks have revealed that, in many cases, attackers can compromise systems without exploiting known vulnerabilities. At BlackHat Europe 2023, a SafeBreach security researcher presented a study on new process injection techniques that leverage Windows Thread Pools to execute malicious code without being detected.
The study analyzed whether:
- A legitimate operating system function could be exploited to execute an injection of
- The most advanced EDR solutions were able to differentiate between legitimate and malicious use of a function.
- Current detection methods were generic enough to identify various variants of this type of attack.
During the investigation, the expert identified eight new process injection techniques.
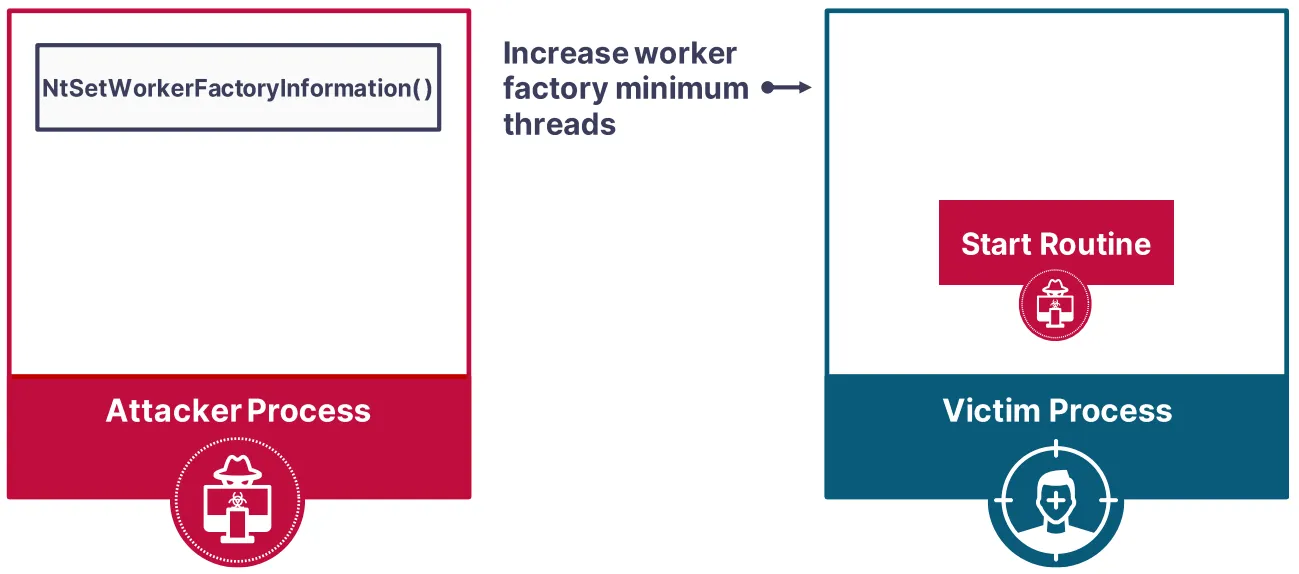
To demonstrate its feasibility, a tool called PoolParty was used, which uses Windows Thread Pools as an attack vector for process injection. This tool can be easily downloaded and run on a test system, confirming that these techniques can trigger malicious execution from a legitimate action, making them even more dangerous.
The most worrying thing was that these techniques were completely undetectable when evaluated against five of the leading cloud-based NGAV/EDR solutions.
What Does this Mean?
Neither more nor less than the evaluated security systems failed to effectively distinguish between legitimate and malicious use of an operating system function, causing attacks to go unnoticed.
A Truth on the Table: Traditional Security Solutions are not Enough
This finding confirmed that current detection approaches are not capable of generically identifying new process injection techniques. This leaves a critical gap in the protection of OT systems, allowing sophisticated threat actors to develop innovative methods to evade traditional security solutions.
Specifically, SafeBreach Labs experts concluded that:
- Current cybersecurity solutions have limitations in the detection of advanced process injection techniques. While EDRs have evolved, their detection approach is not generic enough to identify unknown attack variants. And, in addition, “a lthough we have demonstrated how Thread Pools can be exploited, attackers will undoubtedly find other similar functions to take advantage of. We believe it is essential that EDR vendors develop and implement a generic detection approach to proactively defend against these threats.”
- An anomaly-based approach is needed instead of relying solely on signatures and blacklists. The research showed that executing code on behalf of a trusted process can go unnoticed by an EDR, highlighting the importance of conducting a deeper analysis of process behavior.

Towards a New Generation of Defenses in OT Cybersecurity
To mitigate this threat, researchers pointed to the need for a more generic and anomaly detection-based approach, rather than relying on specific rules or process identity. And the new generation of cybersecurity defenses in industry must be able to protect against attacks never seen before, 0-days and even before attackers conceive them.
Therefore, as soon as the investigation was made public, tests were carried out with a system protected by AZT PROTECT. As a result, this protection system automatically detected and blocked all variants of the attack before they could be executed, without the need for cloud updates, special configurations or additional improvements.
Why Did it Work this Time?
AZT PROTECT protection was effective because it uses a patented approach to protect critical applications against exploitation, blocking the execution of 0-day malware and automatically stopping even the most advanced techniques.
Its deployment is done in a matter of minutes, providing immediate protection without the need for complex configurations.
What Makes it Different?
- AZT PROTECT is compatible with completely isolated (air-gapped) and critical devices based on obsolete or unsupported operating systems, as well as the latest ones.
- It does not interrupt or slow down essential processes, consuming less than 2% of a CPU core and less than 100 MB of memory.
- Its implementation does not require reboots or constant pattern and/or IOC updates.
- It does not try to identify malicious code, but focuses on identifying legitimate executions of the equipment and blocking everything else.
This approach makes it the ideal protection for industrial equipment, without false positives or any of the inconveniences caused by traditional solutions (NGAV/EDR/XDR).
La investigación de BlackHat Europe 2023 deja en evidencia que las soluciones de seguridad tradicionales ya no son suficientes. Si los atacantes pueden infiltrarse sin ser detectados, seguir confiando en los mismos métodos ya no es una opción.





